Renee Dudley on how to trace seemingly impossible financial transactions.
“Following the money trail in the ransomware economy is notoriously difficult, but it’s not impossible. Cryptocurrency tracing firms can help show where ransom payments end up.”
What were the major findings of your story?
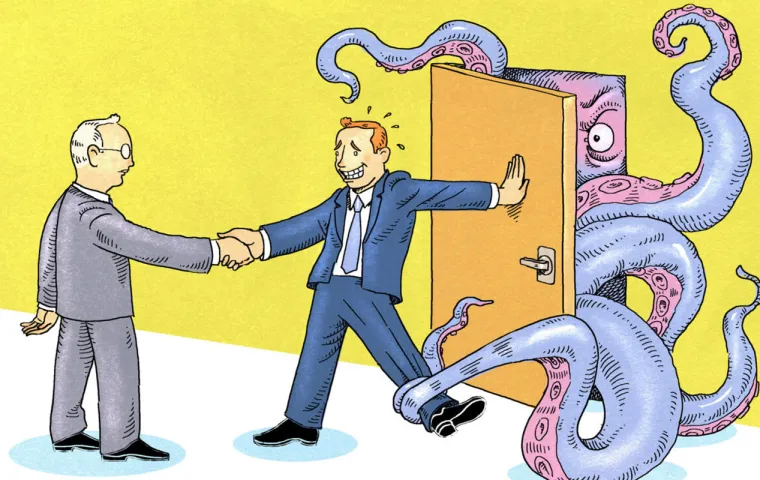
“The Extortion Economy” series examined for the first time the ways that American industries, from data recovery firms to insurers, have abetted the rise of ransomware for their own profit.
What impact did your story have?
We put a spotlight on cybercrime enablers – like data recovery firms – that now are at the center of a national conversation on ransomware. We also highlighted the work of volunteer ransomware fighters.
Did you receive any funding to do the story?
Yes, from ProPublica, where I am a staff reporter.
How did the story start and how did your team decide on the first steps to take in working on this story?
In mid-2018, I began to notice many daily news stories on ransomware. I looked at federal crime data, which suggested that ransomware was being underreported. My editor and I decided we should look into the reasons for that. We sensed that there was an American connection to ransomware beyond victims – a hunch that proved correct when I began reporting on the data recovery industry.
How long did it take to report, write and edit this story?
I started reporting in August 2018. The series included six stories published between May and December 2019.
What challenges did your team face while working with sources?
I had heard from a source that some data recovery firms were misleading victims by telling them they could unlock their ransomware-encrypted files without paying a ransom. These firms obviously did not want their “trade secret” made public. We proved the deception by talking to former employees, tracing payments made to hackers’ bitcoin wallets and reviewing public records. The firms we reported on were paying the ransom without telling victims while also charging a hefty fee on top.
What resources and tools did your team find useful? How did you organize your data and documents?
Some clients of the data recovery firms we reported on had public-sector clients, such as local police departments, whose records are public. I submitted records requests for their contracts and correspondence with the firms, which helped to prove the deception. We used the analysis of a bitcoin tracing company to show that the firms were making ransom payments to known hacker wallets. I also reviewed SEC filings such as 10-Ks, 10-Qs and 8-Ks to show how public companies handle attacks.
What advice would you give journalists working on similar investigations?
1) Set up Google Alerts for topics you’re interested in, then read the results daily. I had one for “ransomware” and read the resulting research papers, news articles, and blog posts each day. This research helped me find sources and generate ideas.
2) Use LinkedIn as a way to find and reach out to sources.
3) Following the money trail in the ransomware economy is notoriously difficult, but it’s not impossible. Cryptocurrency tracing firms can help show where ransom payments end up.
Did your team face any pushback during or after the publication of this story? If so, how did you address this?
One source involved, who agreed to talk on the record at the outset, became nervous as publication neared and wanted to back out. Over the course of several phone calls, I kept this person on board by explaining how the story was contributing to the public interest by describing for the first time the workings of an industry most people had never heard of.